Cybersecurity in NEMT: HIPAA Compliance, Breach Costs, and Practical Defenses

Medical transportation is a part of the broader healthcare industry, which is becoming increasingly digitized. This process raises the efficiency of the system and improves healthcare outcomes for patients, but at the same time makes every stakeholder susceptible to cybercriminal attacks. Many providers handle protected health information at scale, but as small businesses, they do not have the necessary resources to establish appropriate cybersecurity protocols. This article covers the cyber threat environment within the NEMT industry, compliance obligations, breach costs, and suggests defenses that work even without a dedicated IT team.
Contents:
- Why NEMT Providers Are Targets of Cybercriminals
- Compliance Standards in Cybersecurity: HIPAA for Professionals
- The NEMT Cyberthreat Landscape
- What Is the True Price of an NEMT Cyberattack
- Cyberdefenses that Work, Even without a Dedicated IT Team
Why NEMT Providers Are Targets of Cybercriminals
According to the IBM Cost of a Data Breach Report, healthcare is the most expensive industry for data breaches for the 14th consecutive year, averaging around $8-10 million per breach. Therefore, healthcare organizations are among the most frequently targeted sectors globally.
So what are these attacks after? Cybercriminals aren't picky about their targets. Any business with a weak password, an unpatched system, or an untrained employee is an opportunity. For companies outside of healthcare, the worst-case scenario is a ransomware attack that locks them out of their own data until they pay, a breach that leaks company files, or drains a bank account. That's bad enough indeed. But NEMT operators carry something much more valuable than corporate secrets: they can expose up to 20 personal health information data points of every patient they've ever transported.
A complete medical record sells for $250 to $1,000 on the dark web versus $1 to $5 for a stolen credit card number. A person can cancel a credit card, but not their Social Security number, DOB, insurance IDs, or medical histories. Possession of this data enables identity theft, insurance fraud, and prescription fraud at the same time.
Compliance Standards in Cybersecurity: HIPAA for Professionals
The high value of this information is precisely why federal law treats patient data differently from any other business information. And that is why medical transportation stakeholders are subject to the same HIPAA compliance (Health Insurance Portability and Accountability Act) obligations as hospitals. They must protect protected health information (PHI). To do so, NEMT providers are required to implement administrative, physical, and technical safeguards, such as encryption, access control, and audit controls.
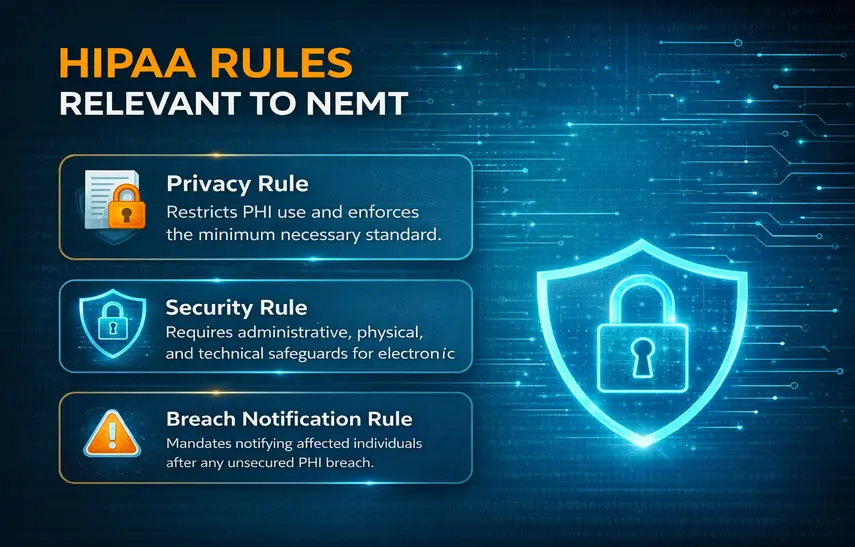
HIPAA establishes three rules that apply directly to medical transportation.
- The Privacy Rule limits the use and disclosure of health information without patient authorization. This rule also establishes the minimum necessary standard (covered entities must limit PHI access to only what each employee needs to do their job). A driver doesn't need a patient's full medical history. A dispatcher doesn't need their insurance billing codes.
- The Security Rule mandates administrative, physical, and technical safeguards for electronic PHI.
- The Breach Notification Rule requires covered entities and business associates to notify affected individuals after any unsecured PHI breach.
If these rules are violated, the penalties can be steep and run across four tiers (2026 inflation-adjusted figures, HIPAA Journal):
|
Tier |
Culpability |
Per violation |
Annual cap |
|
Tier 1 |
Did not know / could not have known |
$145–$73,011 |
$2,190,294 |
|
Tier 2 |
Reasonable cause (not willful neglect) |
$1,461–$73,011 |
$2,190,294 |
|
Tier 3 |
Willful neglect, corrected within 30 days |
$14,602–$73,011 |
$2,190,294 |
|
Tier 4 |
Willful neglect, not corrected |
$73,011–$2,190,294 |
$2,190,294 |
Criminal penalties are also possible and are administered by the DOJ. They can reach $250,000 and 10 years imprisonment for violations involving intent to sell or misuse PHI (AMA).
The NEMT Cyberthreat Landscape
To understand how to protect your business from cybercriminals, we must first identify which attack vectors they usually choose. Surprisingly, most of the successful breaches have nothing to do with sophisticated decryption algorithms or brute force hacking that require immense computational power. The reality is much more prosaic: almost always, it is human error.
Phishing
Phishing is a social engineering attack where criminals send emails, texts, or messages that appear to come from a trusted source (a broker, a software vendor, a colleague) to trick employees into clicking a malicious link, downloading malware, or handing over login credentials. It requires no technical sophistication to execute, which is why it remains the most common entry point into healthcare systems. Healthcare has the highest phishing susceptibility of any industry globally; nearly half of untrained employees will click a simulated phishing email. Phishing remains one of the most successful initial access vectors, particularly in untrained environments.
Ransomware and malware
What starts as a phishing attack when a harmful link is clicked by an employee can transition to a ransomware and malware vector. Ransomware is malicious software that encrypts a victim's files or locks them out of their own systems until a ransom is paid. Malware is the broader category, any software designed to damage, disrupt, or gain unauthorized access to a system. 67% of healthcare organizations were hit by ransomware in 2024, up from 60% in 2023 and 34% in 2021.
Hacking, business associates, and data in transit
Hacking refers to unauthorized access to a system or network, typically by exploiting stolen credentials, brute force attacks (“guessing” generic or weak passwords), unpatched software vulnerabilities, or misconfigured remote access tools. In 2024, 81.2% of all reported healthcare breaches were hacking or IT incidents.
Additionally, for the NEMT industry to perform its duties, it must exchange PHI on a regular basis. This workflow opens up the data-in-transit risk. A single trip's PHI crosses a broker portal, dispatch platform, driver app, billing system, and often a state Medicaid clearinghouse. Information sent through unsecured networks or unapproved channels is vulnerable to being accessed or altered before it reaches its destination, so proper encryption of this data-in-transit is non-negotiable.
Lost devices and Insider threats
Lost and stolen devices are also a risk, though easier to manage. In recent years, modern device encryption protocols have provided reliable protection from data leaks from phones and laptops.
On the other hand, intentional insider threats are still a problem. A disgruntled employee can copy patient records before resigning, forward PHI to personal devices, manipulate trip logs to enable billing fraud, or simply sell login credentials to an outside attacker. Small providers rarely have the audit logging needed to catch slow, low-volume data theft before significant damage is done.
What Is the True Price of an NEMT Cyberattack
The numbers are worth knowing, but the timeline is what catches most operators off guard. Healthcare breaches take an average of 279 days to identify and contain, the longest of any industry.
For smaller healthcare organizations, the Ponemon/Proofpoint study put the average cost of the most expensive single cyberattack at $4.74 million, broken down across three buckets:
- $1,469,524 in operational disruption and system downtime
- $995,484 in lost productivity
- $853,272 in costs to correct the impact on patient care
That last line item is extremely detrimental to the healthcare system. For an NEMT provider, a cyber attack doesn't just freeze the computer system. NEMT providers may:
- incur broker penalties
- face contract termination
- trigger Medicaid audits
- disrupt cash flow and diminish NEMT profits
But the most harmful effect is the missed healthcare appointments. When dispatch goes down, trips don't run. Dialysis patients miss treatments. Chemotherapy patients miss infusions. The Ponemon/Proofpoint 2025 study found 72% of healthcare organizations that experienced a cyberattack reported disruption to patient care, and only 12% of organizations achieved full recovery in the 2024 study, with most taking over 100 days.
Cyberdefenses that Work, Even without a Dedicated IT Team

The good news is that the most effective cybersecurity measures aren't complicated or expensive. They require consistency more than technical expertise. Here's what the data shows actually moves the needle.
1. Employee training
Employees are both the most common entry point for attackers and the most cost-effective defense to invest in. KnowBe4's report found that healthcare's 41.9% baseline phishing failure rate drops to 4.1% after 12 months of ongoing training. An 86% reduction is not a marginal improvement. It's the difference between nearly half your staff clicking a malicious link and almost none of them doing so.
Training doesn't need to be a full-day seminar, but it must be regular. Short sessions covering password hygiene, how to spot phishing emails, safe handling of patient data, and what to do when something looks wrong are enough to change behavior.
2. Multi-factor authentication
MFA is the single highest-return security investment available to a small operator. Microsoft's research found accounts with MFA enabled are more than 99% less likely to be compromised.
3. Role-based access control (RBAC) and vendor reliability
Alongside MFA, role-based access control (RBAC) limits what each employee can see based on their actual job. A driver doesn't need access to billing records. A dispatcher doesn't need full patient medical histories. Restricting access by role is how operators satisfy HIPAA's access control and minimum-necessary requirements, and it's a practical limit on how much damage any single compromised account can do.
Your security posture is only as strong as your weakest vendor. Work with companies that follow sound cybersecurity practices, limit what PHI you share with business associates, and document those obligations through HIPAA-required business associate agreements (BAAs).
4. Data encryption and access controls
Encryption ensures that data intercepted in transit or on a lost device is unreadable without the decryption key. Under HIPAA's encryption safe harbor (45 CFR § 164.402), a lost encrypted device is not a reportable breach: a meaningful legal protection for operators whose drivers carry tablets or phones with PHI. For data in transit, HIPAA's Security Rule treats encryption as an "addressable" specification, meaning you must implement it or document why an equivalent alternative is in place.
5. Patching and cybersecurity software
Outdated software is consistently one of the top entry points for attackers. The Verizon 2025 DBIR found that exploitation of known vulnerabilities now accounts for 20% of all breaches, up 34% year-over-year. Keeping your dispatch software, billing system, driver app, and any connected devices current is not an IT luxury. It's a baseline requirement.
Beyond the basics, dedicated security tools add meaningful protection. Firewalls filter what traffic reaches your network, antivirus software catches known malware before it executes, and endpoint protection covers the individual devices, laptops, tablets, and phones that your team uses in the field and the office. None of these are substitutes for good habits, but they catch what human behavior misses.
6. Incident response planning and backup
Having a plan before something goes wrong cuts breach costs by 58%. An incident response plan doesn't have to be elaborate. It should cover how to isolate affected systems, who to notify internally and externally, how to preserve evidence, and how to communicate with brokers and patients during an outage. Moreover, a company should maintain reliable backups (preferably in the cloud, not local servers) to restore operations quickly, even in the case of a successful cyberattack.
7. Use secure medical transportation software
Every security measure in this article assumes your underlying platform is doing its part. If your dispatch, scheduling, and billing data is flowing through software that isn't HIPAA-compliant, no amount of employee training or MFA will fully close that gap. The first step is making sure the tools your team uses every day meet the baseline. RouteGenie is built on Amazon’s AWS servers with HIPAA-required safeguards already in place: encrypted transmission, access controls, and audit logging by design. See how RouteGenie works.
About the author

As RouteGenie's Marketing Director, Yurii gained deep knowledge in the NEMT industry. He is an expert in marketing, leveraging all channels to build RouteGenie's brand and ensure NEMT providers have access to powerful NEMT software that can boost their growth. Yurii shares his knowledge by writing content on marketing and healthcare topics, including medical transportation, home care, and medical billing.